How to store encryption key in database images are ready in this website. How to store encryption key in database are a topic that is being searched for and liked by netizens today. You can Find and Download the How to store encryption key in database files here. Download all free vectors.
If you’re searching for how to store encryption key in database pictures information connected with to the how to store encryption key in database keyword, you have visit the right site. Our site frequently provides you with hints for viewing the maximum quality video and image content, please kindly surf and find more informative video content and images that match your interests.
20082014 Otherwise it would be easy to find all the common data in a database and deduce a pattern from the encryption. 23022018 If what you provide the user is a combination of primary key and API key you can then securely store the API key. To get a separate key. To safely store your data in a database youd start by generating a strong secret key. Let encrypted cipherupdatesourceData binary binary.
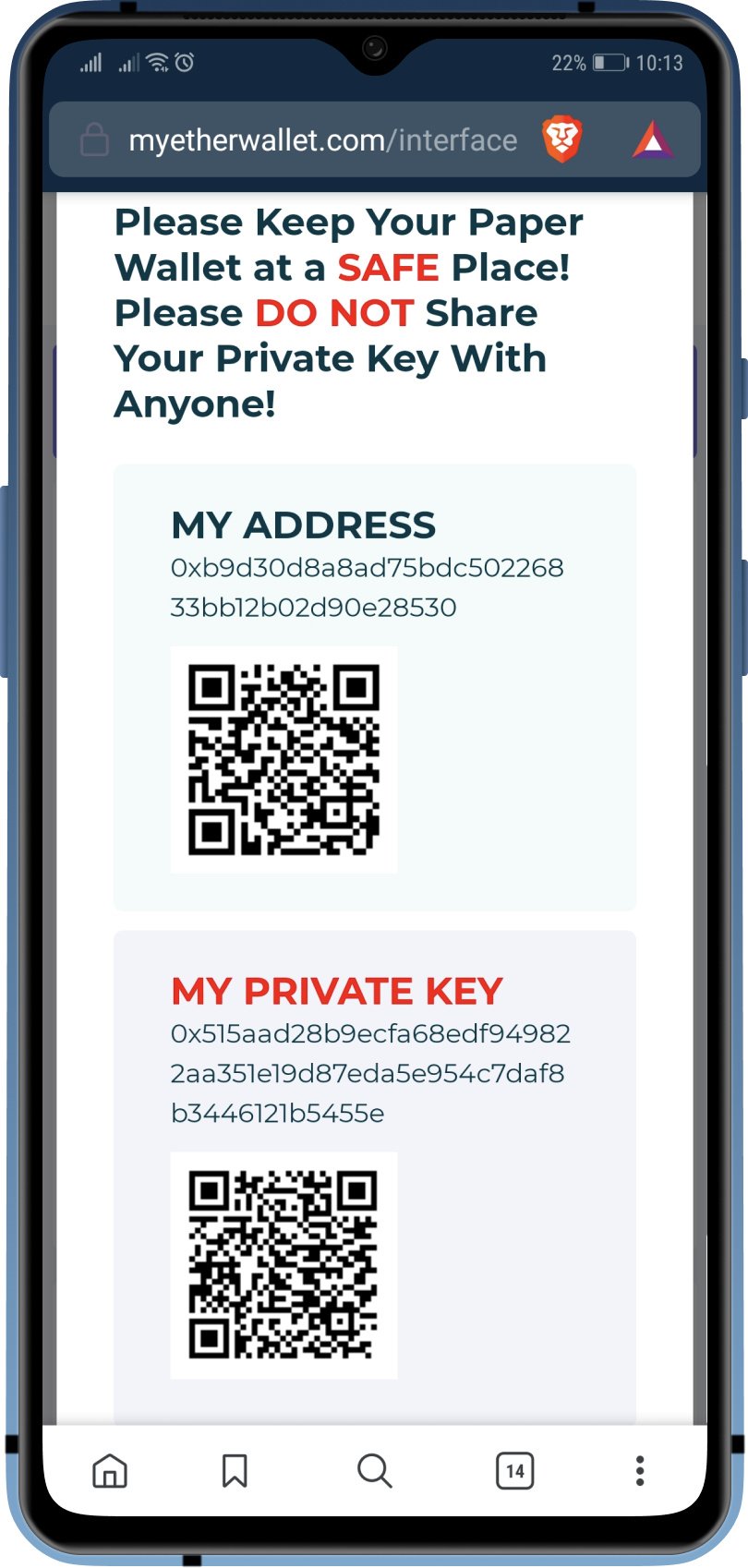
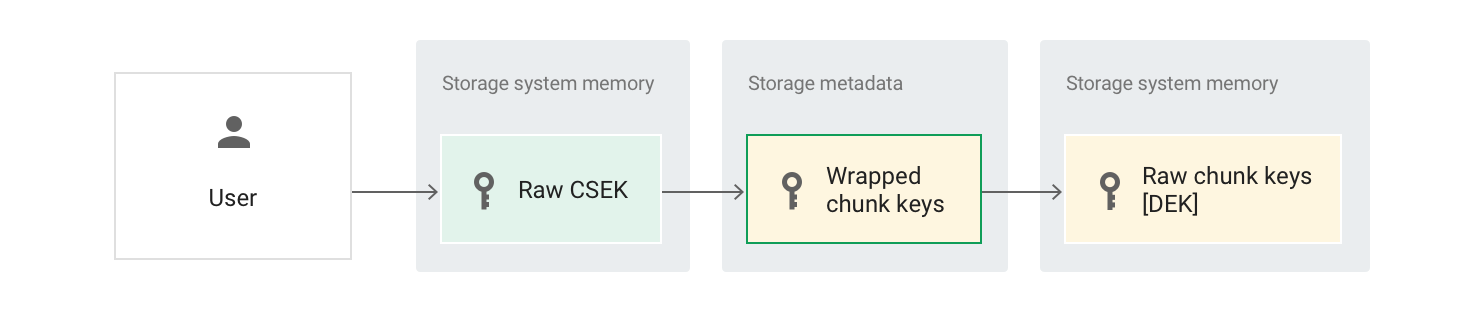
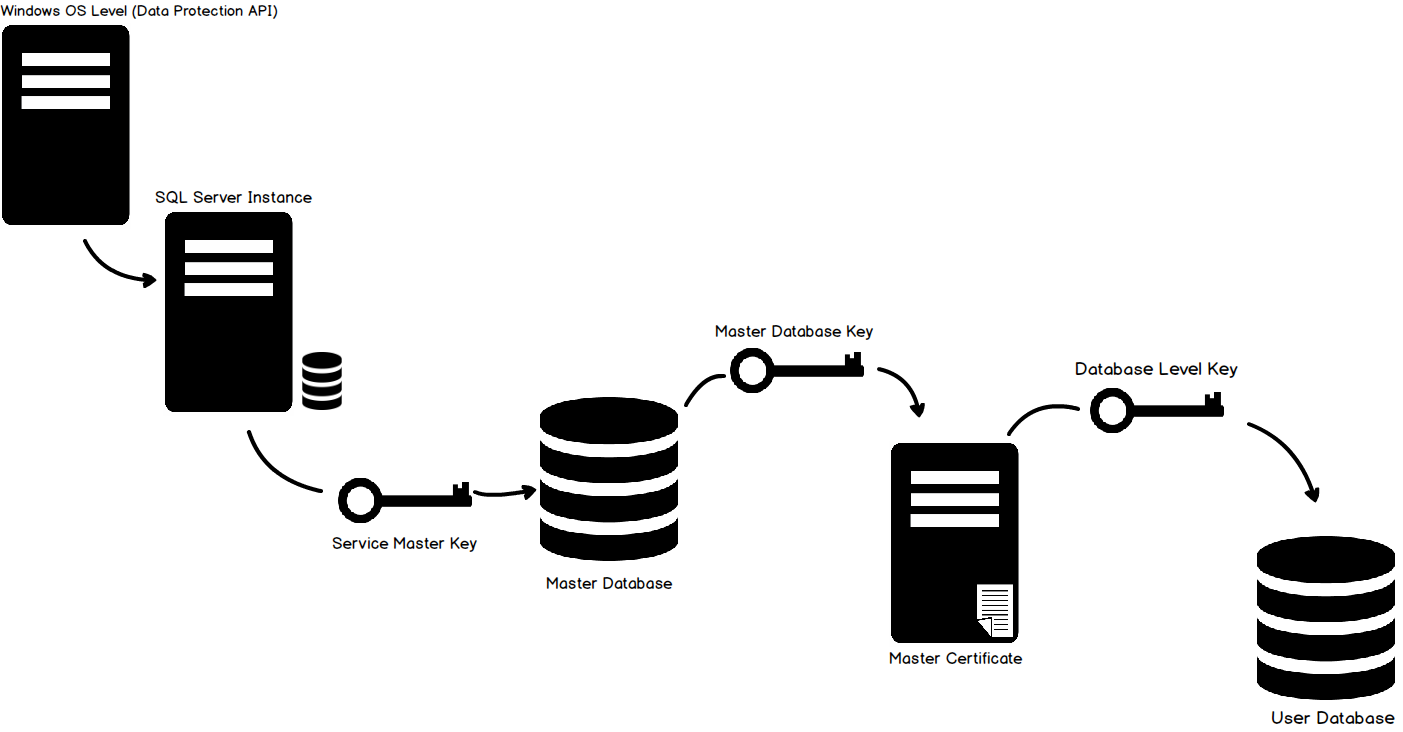
How To Store Encryption Key In Database. Then use that as key for encrypting the private key. 23042020 The Master Key Configuration page is where you set up your CMK and select the key store provider where the CMK will be stored. Currently you can store a CMK in the Windows certificate store Azure Key Vault or a hardware security module HSM. 05112019 A better scenario would be to collect names mails and phone numbers encrypt and store them in a database hosted on a server different than the web server.
 Transparent Data Encryption From docs.oracle.com
Transparent Data Encryption From docs.oracle.com
To get a separate key. The copy of the DMK stored in the master system database is silently updated whenever the DMK is changed. 23042020 The Master Key Configuration page is where you set up your CMK and select the key store provider where the CMK will be stored. You must have an encryption key to decode the encrypted data. 10112008 If you need the registry key as well you can always use the following connection string. 20082014 Otherwise it would be easy to find all the common data in a database and deduce a pattern from the encryption.
Remember to use the algorithm correctly.
07052019 Now we can use the generated key to encrypt any data. Database encryption is. Since the key is effectively a password hashing should be sufficient and is recommended. Putting the encryption key anywhere in the database or accessible to the database frequently defeats the purpose of encryption because anyone with access to the database can simply decrypt the data. There are different hashing algorithms. You must have an encryption key to decode the encrypted data.
 Source: docs.oracle.com
Source: docs.oracle.com
The encryption keys should be stored at. 05112019 A better scenario would be to collect names mails and phone numbers encrypt and store them in a database hosted on a server different than the web server. Initialization vector const cipher cryptocreateCipherivaes-192-cbc keycipherKey iv. Generally hashing requires a salt for each record. To safely store your data in a database youd start by generating a strong secret key.
 Source: docs.mongodb.com
Source: docs.mongodb.com
Now Oracle also supports the integration with the OCI Vault Service where you are able to create and control your TDE master encryption keys or import your existing ones. 05112019 A better scenario would be to collect names mails and phone numbers encrypt and store them in a database hosted on a server different than the web server. Government regulations including HIPPA require some forms of private or sensitive data to be transmitted in encrypted form. To get a separate key. 06092021 Data in an AIS database can be stored in encrypted form to deter it unethical or fraudulent use.
 Source: stackoverflow.com
Source: stackoverflow.com
Putting the encryption key anywhere in the database or accessible to the database frequently defeats the purpose of encryption because anyone with access to the database can simply decrypt the data. 10112008 If you need the registry key as well you can always use the following connection string. 14032017 To enable the automatic decryption of the database master key a copy of the key is encrypted by using the SMK. 23042020 The Master Key Configuration page is where you set up your CMK and select the key store provider where the CMK will be stored. 20082014 Otherwise it would be easy to find all the common data in a database and deduce a pattern from the encryption.
 Source: cloud.google.com
Source: cloud.google.com
Remember to use the algorithm correctly. How to store encryption keys for example in the files. The encryption of this data consists of using an algorithm to convert text or code for it to be unreadable. If Oracle permissions are enough to prevent the user from decrypting the data they would be enough to prevent the user from selecting the unencrypted data. The encryption keys should be stored at.
 Source: documentation.commvault.com
Source: documentation.commvault.com
Database encryption is. The copy of the DMK stored in the master system database is silently updated whenever the DMK is changed. A valid connections string that re-directs to a file on disk. The encryption keys should be stored at. To get a separate key.
 Source: sqlshack.com
Source: sqlshack.com
Database encryption is. The copy of the DMK stored in the master system database is silently updated whenever the DMK is changed. Government regulations including HIPPA require some forms of private or sensitive data to be transmitted in encrypted form. Ie it is clear that you can throw on the disc but in the event of a compromise of access together with the base leaked key. The encryption keys should be stored at.
 Source: thesslstore.com
Source: thesslstore.com
05112019 A better scenario would be to collect names mails and phone numbers encrypt and store them in a database hosted on a server different than the web server. The encryption of this data consists of using an algorithm to convert text or code for it to be unreadable. Currently you can store a CMK in the Windows certificate store Azure Key Vault or a hardware security module HSM. The encryption keys should be stored at. 10112008 If you need the registry key as well you can always use the following connection string.
 Source: docs.microsoft.com
Source: docs.microsoft.com
Putting the encryption key anywhere in the database or accessible to the database frequently defeats the purpose of encryption because anyone with access to the database can simply decrypt the data. Database encryption is. Currently you can store a CMK in the Windows certificate store Azure Key Vault or a hardware security module HSM. 23042020 The Master Key Configuration page is where you set up your CMK and select the key store provider where the CMK will be stored. If Oracle permissions are enough to prevent the user from decrypting the data they would be enough to prevent the user from selecting the unencrypted data.
 Source: docs.oracle.com
Source: docs.oracle.com
This protects against offline attacks unless they capture the key out of RAM which is tougher to do. You must have an encryption key to decode the encrypted data. Currently you can store a CMK in the Windows certificate store Azure Key Vault or a hardware security module HSM. This tutorial shows how to store your keys in the Windows certificate store. A valid connections string that re-directs to a file on disk.
 Source: info.townsendsecurity.com
Source: info.townsendsecurity.com
Initialization vector const cipher cryptocreateCipherivaes-192-cbc keycipherKey iv. Putting the encryption key anywhere in the database or accessible to the database frequently defeats the purpose of encryption because anyone with access to the database can simply decrypt the data. It is stored in both the database where it is used and in the master system database. There are different hashing algorithms. 06092021 Data in an AIS database can be stored in encrypted form to deter it unethical or fraudulent use.
 Source: docs.mongodb.com
Source: docs.mongodb.com
Let encrypted cipherupdatesourceData binary binary. 23042020 The Master Key Configuration page is where you set up your CMK and select the key store provider where the CMK will be stored. To safely store your data in a database youd start by generating a strong secret key. Let encrypted cipherupdatesourceData binary binary. Ie it is clear that you can throw on the disc but in the event of a compromise of access together with the base leaked key.
This site is an open community for users to share their favorite wallpapers on the internet, all images or pictures in this website are for personal wallpaper use only, it is stricly prohibited to use this wallpaper for commercial purposes, if you are the author and find this image is shared without your permission, please kindly raise a DMCA report to Us.
If you find this site good, please support us by sharing this posts to your favorite social media accounts like Facebook, Instagram and so on or you can also save this blog page with the title how to store encryption key in database by using Ctrl + D for devices a laptop with a Windows operating system or Command + D for laptops with an Apple operating system. If you use a smartphone, you can also use the drawer menu of the browser you are using. Whether it’s a Windows, Mac, iOS or Android operating system, you will still be able to bookmark this website.